This is an English translation of the original German article. Translation by Anna Biselli.
Extended Specialist Support Internet
In June 2014 NDR, WDR and SZ and the newspaper Neues Deutschland reported about a new department at the German domestic security agency Federal Office for the Protection of the Constitution (Bundesamt für Verfassungsschutz, BfV): The Extended Specialist Support Internet (Erweiterte Fachunterstützung Internet, EFI). In February 2015 we published an excerpt of the agency’s budget plan for „Bulk Data Analysis of Internet Content“. Hans-Christian Ströbele, Green member of Federal Parliament, followed up on our report and questioned the German Federal Government about it – calling this kind of internet surveillance „illegal“ and „unlawful“.
Now we received the internal BfV concept document of the new unit labeled „confidential“, which we hereby publish in full: Concept for the implementation of department 3C „Extended Specialist Support Internet“ in the BfV.
And while we’re on it, we also publish the human resources plan: Personnel Plan of department 3C „Extended Specialist Support Internet“ in the BfV.
Extending internet surveillance
This is what it’s all about:
With the implementation of department 3C we aim at to improve and extend communication surveillance of internet-based individual communication within the scope of the G‑10-law (Federal wiretap law similar to IPA in Britain and FISA in the USA). Unit 3C is also supposed to analyze all kinds of data obtained by the BfV from various sources. In the digital age, this data often cannot be analyzed manually anymore. Besides that, 3C will deal with new methods and measures for data analysis that require advanced technical expertise as well as a classification in a complex legal framework, without G‑10 being relevant.
Six units, 75 permanent positions
The new department 3C is part of Section 3 Central Specialist Support and consists of six units:
- Unit 3C1: Policy, Strategy, Law
- Unit 3C2: Content and technical analysis of G‑10 internet information (Cologne)
- Unit 3C3: Content and technical analysis of G‑10 internet information (Berlin)
- Unit 3C4: Central data analysis (Cologne)
- Unit 3C5: Central data analysis (Berlin)
- Unit 3C6: IT operational measures, IT-forensic analysis
Personnel requirements „amounting to 75 full-time positions“ is calculated. As a first step, an initial team tasked with establishing EFI was set up, consisting of 21 positions. An expansion to „51 permanent positions“ was already planned last year. A further increase to 75 positions with almost 100 tasks is likely taking place right now.
What the domestic security agency is allowed to wiretap

The German domestic security agency is authorized by G‑10-law to derogate the fundamental right to privacy of correspondence, post and telecommunication. The same rules apply to the foreign and military intelligence agencies BND (Federal Intelligence Service) and MAD (Military Shielding Service). But unlike BND, the domestic security agency BfV has to restrict its communication surveillance to individual, suspicion-based cases. Nonetheless, BND collects data from „strategic“ mass surveillance and can legally share that with BfV.
Furthermore, BfV is allowed to gather traffic and inventory data from data retention and inventory data collection.
Finally there is also the covert usage of technical measures like eavesdropping with the help of microphones and cameras. BfV is developing new methods like „covert IT surveillance of online services.“
Bulk analysis of internet content
The domestic security agency emphasizes publicly that it only targets specific individuals. But as we have reported previously, the agency is spending 2.75 millions Euros to gather and analyze vast amounts of internet content:
A system for the collection, processing and analysis of bulk internet data should be developed in cooperation with external partners. This shall enable BfV to analyze bulk data and combine relevant information. The aim is to detect previously unknown and hidden connections between relevant persons and groups on the internet.
This is the task of the new department „Extended Specialist Support Internet“ (EFI).
Surveillance system Perseus

Perseus, son of Zeus, was the first hero in Greek mythology. He has a helm of darkness to hide, winged sandals to fly and a polished shield, which he used to safely approach the monster Medusa and cut off her head.
The BfV now named a system for telecommunication surveillance after him:
As part of the individual, line based communication surveillance the monitoring system PERSEUS helps to process and analyze traditional telephone communication (e.g. voice, fax, SMS) as well as internet communication (e.g. mail, chat protocols, web sessions and file transfers).
Perseus was „planned between 2004 and 2006 and based on the state of the art of the time“. Two years ago, it was „finished with the completion of expansion level 2“. According to BfVs internal budget plan, additional 750.000 Euros were invested only two years ago for an „expansion of input bandwidth“. Since more people transfer constantly growing amounts of data (the agency lists a broad „variety of new services and devices“ like flatrates, smartphones, tablets and IPTV). Because of that, the „input-net-IP-bandwidth to be processed by the monitoring system“ would be increased „to at least 1 GBit/s“.
In the current fiscal year, yet another 3.5 million Euros were allocated „for regular modernization“ of Perseus.
Processing with Perseus and „special tools“
Two new BfV-units in Cologne and Berlin called „content and technical analysis of G‑10 internet information“ will process the surveilled internet data:
A part of the gathered raw data will be provided to the analysts in a readable format after it was automatically pre-processed by PERSEUS. But to find and present specific information emerging from individual surveillance measures (e.g. Facebook chats), special skills in handling PERSEUS and a deeper technological understanding of current internet services are required.
Part of the raw data cannot be automatically decoded by PERSEUS. This data has to be exported and processed with special tools for decoding and analysis. With that, additional insights from already available data of individual surveillance can be processes and prepared made available for analysis.
These units will also „create and maintain complex requests in the analysis system“.
Movement patterns and social network graphs
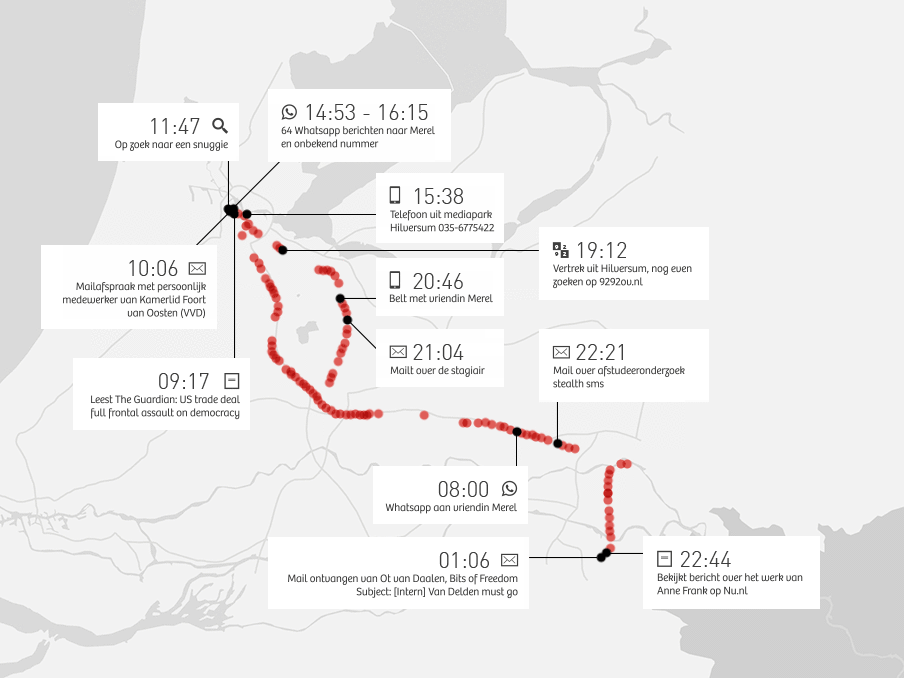
To analyze collected internet data, the security agency uses exactly the capabilities we constantly report about. Two new units for „central data analysis“ combine and process various gathered data pools and generate movement patterns and social network graphs from metadata:
In Cologne and Berlin, units 3C4 and 3C5 shall be extended to central analysis centers in order to satisfy the demands of the specialist departments for the analysis of all relevant insights about monitored individuals (communication behavior, movement patterns, etc.).
They shall create analysis reports for metadata from G‑10-/§8a surveillance measures, f.e. overviews of communication partners and frequencies, well as temporal and spatial distribution of communication. Cross reference analysis can show if multiple persons subject to communication surveillance measures are in contact with each other or with the same intermediary (analysis of social network graphs).
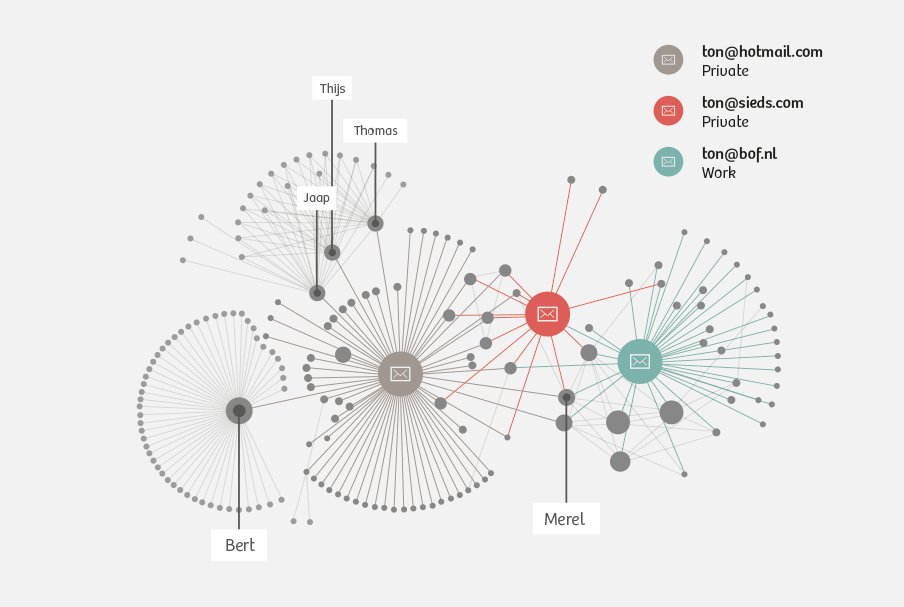
Our most widely read article last year was the analysis of Ton Siedsma’s metadata: How your innocent smartphone passes on almost your entire life to the secret service. Now we can finally verify with original documents that the domestic secret service does exactly what we described.
From a witness in the German Parliamentary Committee investigating the NSA spying scandal we also know that the Federal Intelligence Service creates social network graphs over 5 hops:
Notz: Would you agree that an acquaintance of an acquaintance of an acquaintance of the client of a lawyer is monitored?
F.: Yes.
Covert IT surveillance
Additionally, BfV wants to exploit new data sources for surveillance. The new unit „IT operational measures, IT-forensic analysis“ will develop new surveillance methods:
For the most comprehensive analysis of communication behavior of monitored persons, we need interception methods going beyond source based interception. The „nomadization“ of user behavior, the internationalization of offered services, the encryption of communication as well as the lack of possibilities to oblige foreign providers to cooperate will otherwise leave more and more gaps in the analysis of suspects communication.
Therefore, unit 3C6 will concentrate planning and execution of operational measures for covert information gathering of not publicly available information on the internet. This especially includes covert IT surveillance measures of online services under G‑10 law („server interception“, „surveillance of online forums“, „e‑mail interception“).
Server interception with network taps
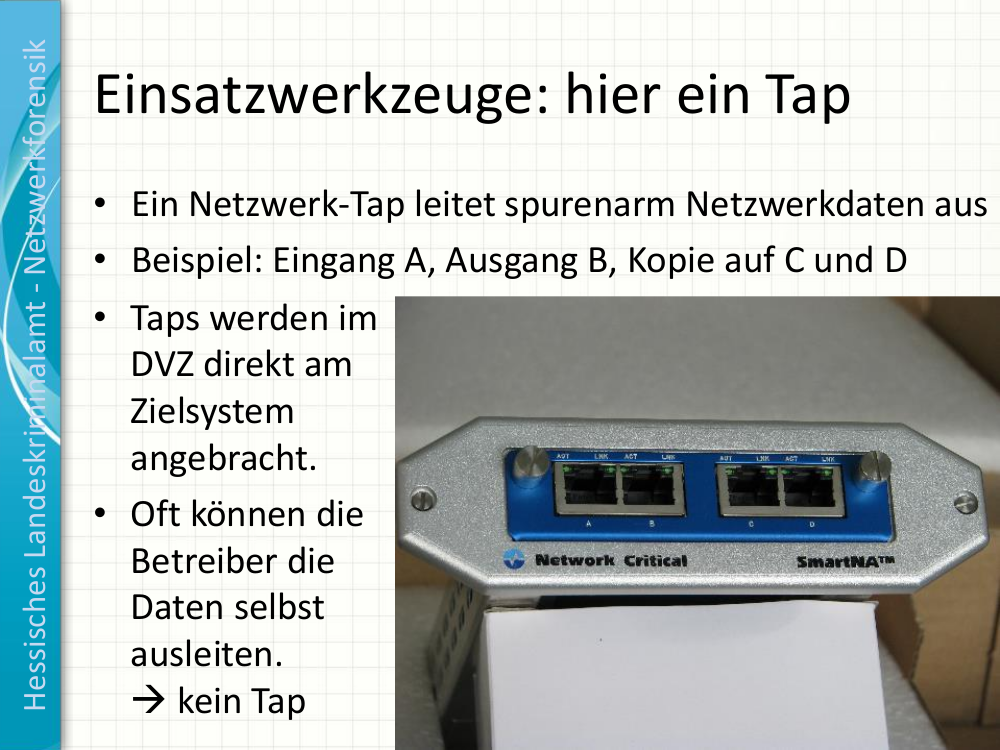
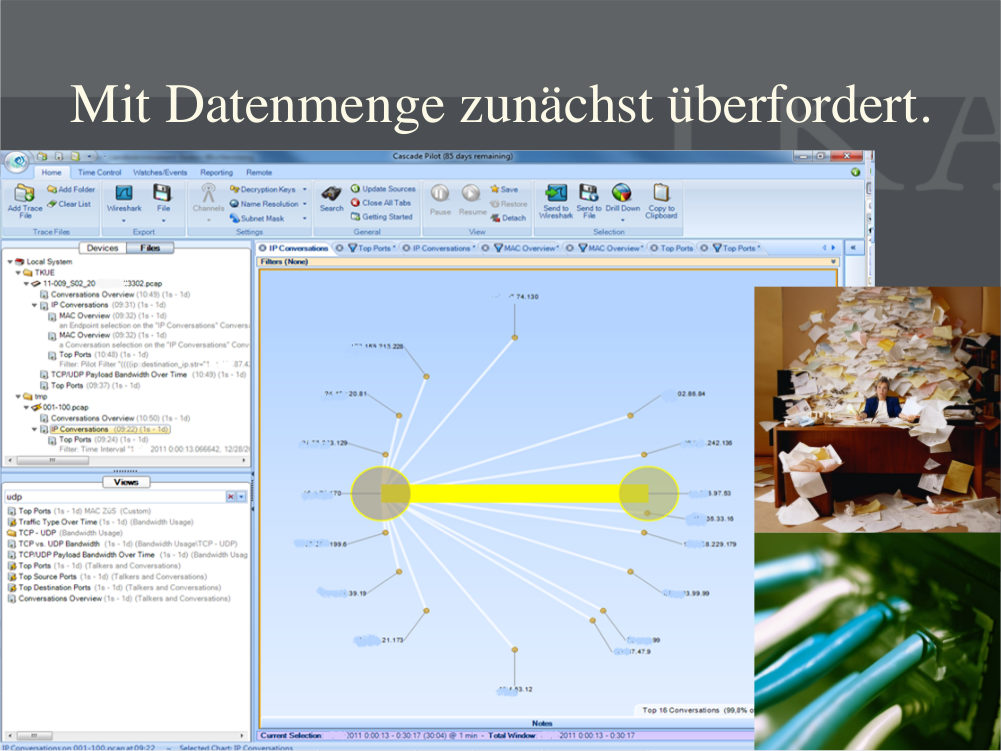
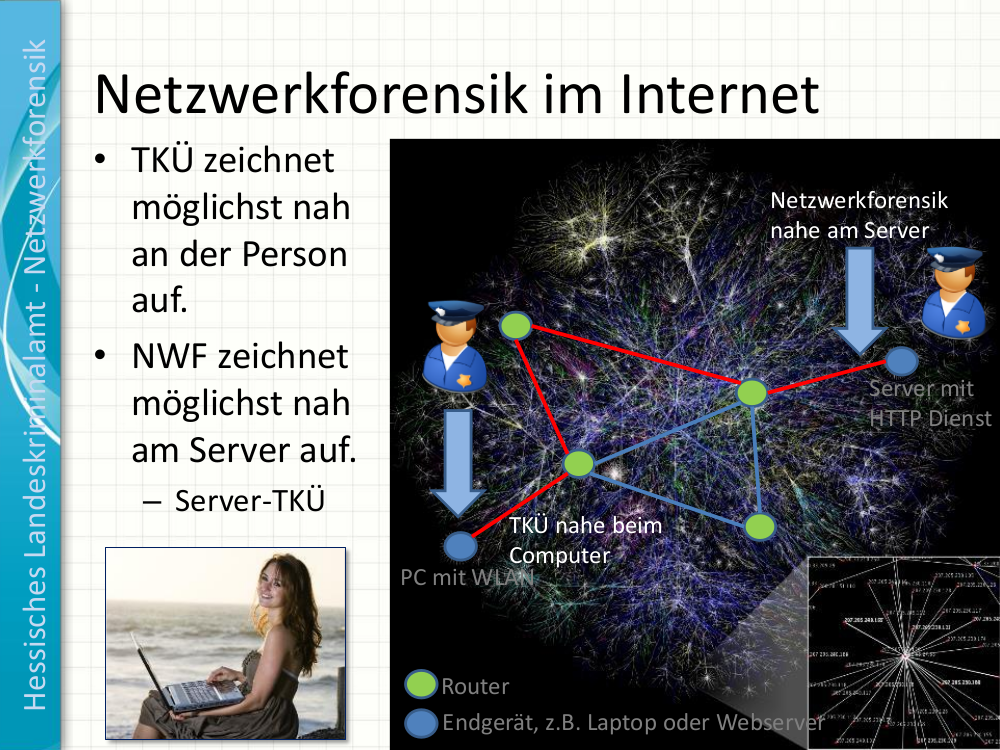
Andreas Frantzen of State Criminal Police Office Hessen presented those surveillance measures at a workshop in December 2013, we are publishing his slides: Network Forensics for Law Enforcement Agencies.
Detlef Borchers summarizes at heise online:
Andreas Frantzen of the Hessian State Criminal Police introduced the audience to network forensics. It’s the counterpart of telecommunication surveillance happening at the users end. While telecommunication surveillance is installed as close as possible to a client, network forensic operates as close as possible to the server.
Network taps intercepting the entire traffic streams are very often installed directly at servers in data centers. Afterwards, data is processed with tools like Wireshark, CascadePilot and RSA Security Analytics Server. Because the emerging data volume is huge, it is important for investigators to prepare the data by intelligent data reduction.
The new unit will plan and develop „IT measures for use in operative measures“ and conduct „operative information gathering“ and „data extraction“ by „unconventional telecommunication surveillance“.
State malware? Unconstitutional.

The „execution of operative measures […] for covert gathering of information in computer networks“ sounds a whole lot like the ever more widely used state malware. Since the ruling of the Federal Constitutional Court in 2008, there is no legal basis for the BfV to use such intrusive measures.
The German Federal Criminal Office however received such an authorization as part of the revision of the law for the Federal Criminal Office in 2008 – with ongoing constitutional complaints still pending. But BfV and BND do not have a legal basis to use state malware, their utilization would be illegal and unconstitutional. This was confirmed to netzpolitik.org by a range of legal experts on the topic.
Currently, the German Government is working on a legal reform of the BfV, which civil rights organizations are criticizing. Moreover, the BfV will also get new authorities with the currently debated IT security law.
Many open questions remain
Twice, we confronted the Federal Office for the Protection of the Constitution with specific questions regarding this article. To this day, one week later, we did not receive an answer. The promised transparency initiative of security services obviously ends with unwanted questions of journalists. We didn’t even receive a standard boiler-plate reply or „neither confirm nor deny“ – nothing.
We also contacted the spokespersons of the parliamentary groups in the committee on internal affairs in the German parliament and asked how they assess scope and authorities of the new department. We updated our original German article with their replies. The two groups that replied – Leftists and Greens, both opposition – called the revelations illegal and unconstitutional and called for the complete dissolution of the German Domestic Secret Service.
Find the leaked documents in full text attached to the original German version of this article.
