Vor einem Monat veröffentlichte das Spiegel-Team unter dem Titel Die NSA rüstet zum Cyber-Feldzug neue Snowden-Dokumente. Unter den insgesamt 36 PDF-Dateien findet sich auch die Analyse eines Trojaners „Babar“ (Mirror), den der kanadische Geheimdienst CSEC der französischen Regierung zuschreibt.
Zwei neue Untersuchungen ziviler Forscher/innen untermauern diese Behauptung jetzt. Marion Marschalek berichtet auf dem Firmen-Blog von Cyphort Labs: Babar: Suspected Nation State Spyware In The Spotlight
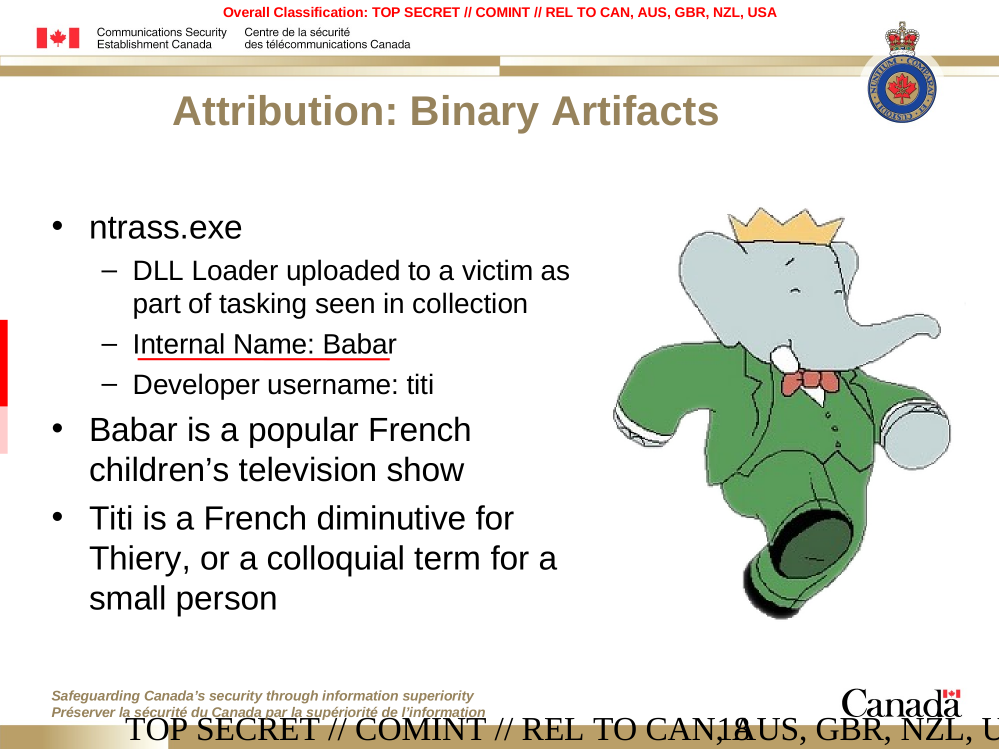
The internal project name of the analyzed malware is „Babar64“, which rings a bell when thinking back of documents leaked through Der Spiegel back in January. There, a slide deck originating from Communications Security Establishment Canada (CSEC) describes an alleged nation state malware named Babar. The samples at hand fit well with what is described in the CSEC document; and, as CSEC states they are suspected to originate from French intelligence.
As it is with binary attribution, these allegations are impossible to prove without the shadow of a doubt. What we can say with certainty though is that Babar strikes the analyst with sophistication not typically seen in common malware. Furthermore, the binaries come with the same handwriting as the malware dubbed „Bunny“ which we have blogged about before. We assume the same author is behind both families.
 Zusammen mit über fünf weiteren Forschern, darunter Morgan Marquis-Boire, veröffentlichte sie gleichzeitig den Bericht „Shooting Elephants“ (No elephants were harmed in the making of this report.) Das PDF ist leider original auf Google Drive, also spiegeln wir es lokal.
Zusammen mit über fünf weiteren Forschern, darunter Morgan Marquis-Boire, veröffentlichte sie gleichzeitig den Bericht „Shooting Elephants“ (No elephants were harmed in the making of this report.) Das PDF ist leider original auf Google Drive, also spiegeln wir es lokal.
The myth of Babar has been around for a while in the intelligence community. Questions have been raised since Le Monde published an article on Babar in 2014 and were recently fuelled by a leaked government presentation found among a stash of documents published in January by Spiegel. The leaked document was authored by the Communications Security Establishment Canada (CSEC) and reports about a potential nation state attack involving malware named Babar. The actor behind the attacks is assumed to be French inteligence. Assumptions are based on certain binary attributes, language and location of infrastructure as well as targets.
The binaries at hand fit well with the description CSEC provides, although it is quite clear they are a newer version from what CSEC had uncovered around 2009. It is not clear whether the compilation timestamps are falsified, but an earlier compilation time than the actual stamp seems unlikely.
Doubtlessly though, the Babar binaries match with a malware strain representing itself as Bunny, as well as a family dubbed NBOT or TFC.
Weitere Erkenntnisse wird die Malware-Forscherin Marion Marschalek im März auf der Konferenz SyScan Singapore präsentieren. Lorenzo Franceschi-Bicchierai hat bei Motherboard eine weitere Zusammenschrift: Meet Babar, a New Malware Almost Certainly Created by France.