Looking to spy on a partner unnoticed? You will find hundreds of apps on the net helping you to do just that. The industry for so-called ‘stalkerware’ is thriving – probably also due to the fact it hardly has to fear criminal prosecution. These apps can be installed unnoticed on a victim’s phone and quietly record everything in the background: from chat messages, emails, photos and browser history to the GPS location.
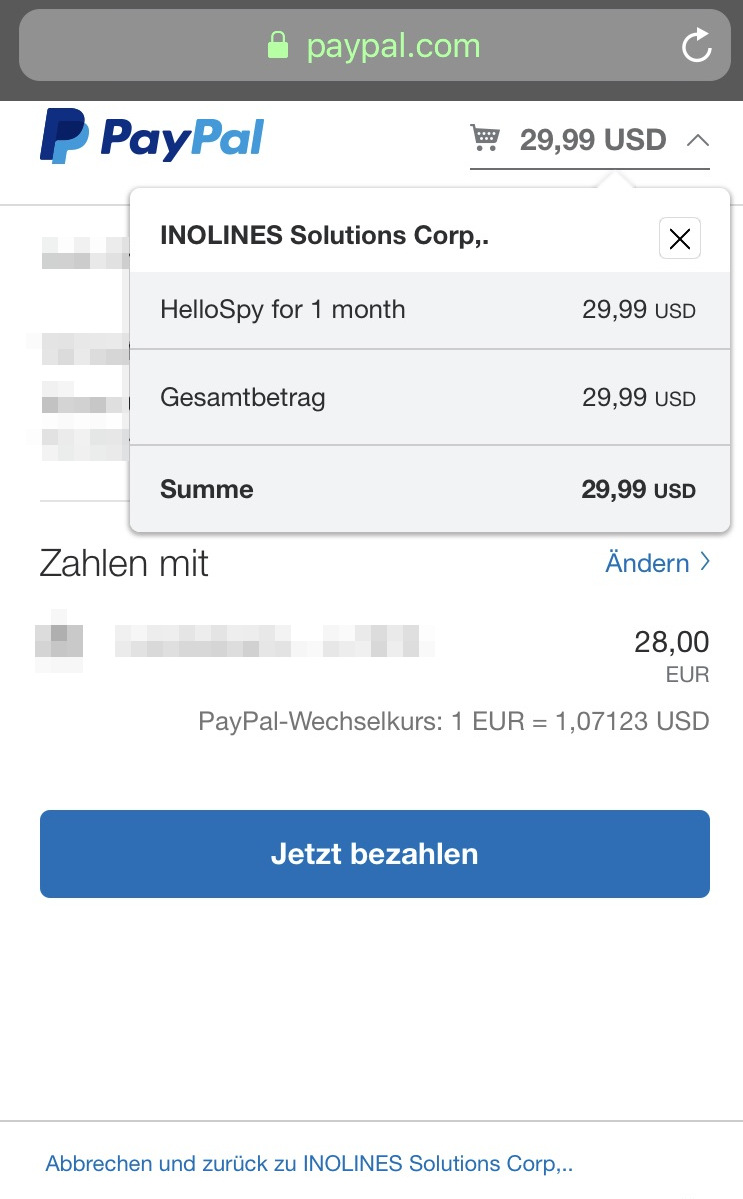
One such app is HelloSpy. Its creator earns his money with the fees of users all over the world, who can spy on their loved ones for the equivalent of just 28 Euros a month. They can conveniently pay for this via Paypal.
Same Old App, new company name
In February Paypal had blocked the account behind HelloSpy after the investigative tech site Motherboard reported on the case. A spokesperson wrote to Motherboard: “Paypal’s policy is not to allow our platform to be used for the sale of services or products that are marketed for illicit purposes.”
Earlier this week netzpolitik.org found it was once again possible to use Paypal to pay for the app via the company’s website. The vendor had simply returned – this time under a new company name. A few hours after netzpolitik.org had asked Paypal for comment, the account was blocked. But just a few days later the vendor is once again back on Paypal – using a new company name once again.
To install HelloSpy, the perpetrator must have physical access to the device for at least a few minutes – usually, this is no problem for a partner. Once the app is on the phone, it can collect all kinds of information in the background without giving any sign of the surveillance. The data is uploaded to a server and from there can be accessed by the perpetrator through the application dashboard in any browser.
The perpetrator can then click through lists of called numbers, photos, videos, chats or the browser history and location data of the victim. According to HelloSpy’s website, even the microphone can be activated remotely, allowing to use the phone as a bug.
The manufacturer’s website openly advertises the product as a solution for spying on allegedly unfaithful partners. „The past two decades have made infidelity easier than ever, especially with the rise of … social networks and mobile phones,“ it says. The page is illustrated with a photo of a woman grabbed by a man on her wrist – her face covered in bruises.
One app blocked, dozens allowed to go on
For Paypal it should not be difficult to recognize that it is the same product they had already banned on the platform for serving an illegal purpose: Spying on another person without their knowledge and consent is a criminal offence in Germany and many other countries.
Even if the manufacturer has re-registered on the platform with a new company name and account details: The website from which he forwards his customers to Paypal is still the same. The name of the product is also clearly visible during the payment process. It’s as if a guest with a house ban simply puts on glasses and a hat and then walks back in through the front entrance. Again and again.
„For privacy reasons, no information“
netzpolitik.org asked Paypal for comment on why such an obvious deception attempt of an already blocked dealer is not being recognized. A spokesperson did not address that question. Instead she referred us to the fact that Paypal, as a credit institution licensed in Luxembourg, is subject to banking secrecy there. „For this reason, as well as for reasons of data protection, we are not allowed to provide information on individual accounts and account holders,“ she wrote in an email.
She also failed to address how Paypal ensures that blocked vendors do not return under a new name. Paypal regularly checks questionable activities to ensure that they do not violate the usage guidelines, she wrote, and that the company reviews flagged accounts and takes action as appropriate. But it’s obvious that whatever Paypal is doing for platform moderation is not enough, and existing loopholes are enabling the developers of stalkerware to continue to exist on the platform.
It’s also unclear why the platform will block payments for HelloSpy while other spy apps from the same manufacturer can still be paid for via Paypal. The security researcher Cian Heasly had discovered that the same manufacturer sells five other apps. He hides behind several company names, but had registered all domains using the same Googlemail account.
About a dozen other Stalkerware manufacturers are currently processing the subscription payments for their services via Paypal, Heasly has shown. Many of them are a lot subtler then HelloSpy and market their products ostensibly as control apps for parents or employers who track employees with their consent – the only two legal use cases.
This so-called dual-use applicability means that numerous apps suitable for stalking can still be found in Apple’s and Google’s app stores, as a team of researchers in the US has shown. The manufacturers claim that the perpetrators alone are responsible for the use of their software for illegal purposes. Like a knife, their technology could be used for good as well as for violent crime.
However, research by the Canadian privacy organization Citizen Lab has shown that even these ostensibly clean companies often aim for a certain clientele: stalking partners. This is indicated by the ads they buy on Google for certain keywords.
One company even placed text in the HTML code of the site that was only visible to search engines and presented the app as a top solution for partner stalking. The manufacturers’ websites also lacked information as to how those affected can protect themselves against the apps or uninstall them.
New methods, old violence
It’s hard to determine how often such apps are being used. As a rule, those affected do not notice that they are being monitored by stalkerware. They can only make assumptions. Women’s counselling centres and shelters however report that digital surveillance in violent partnerships has seen a sharp uptick in recent years. Men followed fleeing partners to the women’s shelter, tracked them with the help of smartphones they gave to their children or confronted them after a visit to the counselling centre.
It is difficult to detect stalkerware on the phone of the victims. Counselling centres lack the expertise and resources to conduct digital forensics. The police have tools for forensic analysis of devices, should a woman dare to file a complaint, but usually declines to do forensics in cases of domestic violence and stalking.
Digital stalking is nothing fundamentally new, experts emphasise: The problem of violence in partnerships is old. Today, violent partners only have new technological possibilities at their disposal to exercise control – and they make use of them. This is partly made possible because Paypal continues to support these business models as a payment service provider.




